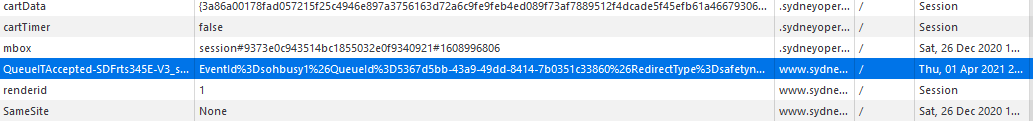
This security vulnerability is easily exploited, without requiring technical skill. Here's how. Visitor A goes through the queue and gets a "secure" validation cookie, and posts the cookie name and value online. Visitor B copies the details and adds them as a new cookie in the browser, which is easy to do (Right Click, Inspect Element, Storage, Cookies, Right Click, Add New). Visitor B can then access any page on your "protected" site, because your webserver thinks Visitor B has been through the queue, even though Visitor B is cheating.

We easily bypassed Queue-it security by copying this cookie from someone who had already been passed by their queue servers. This vulnerability affects the Queue-it Javascript Connector and the Known User Connector that Queue-it advertises as "secure" and "unskippable".
Queue-Fair signs all visitors with code specific to the visitor's browser, which means copied credentials can be automatically detected and unfair access denied.
What's more, Queue-Fair offers a raft of anti-bot measures so you can ensure that it's genuine customers participating in your online event, not bots, scalpers or touts. We operate security checkpoints at both the Join and Pass stages of each visitor's journey through the queue, optionally using Captcha, Proof of Work - and you can limit by IP address too.
Need to restrict your sale to one purchase each? That's easy - we can automatically send people who have already made a purchase to the back of the queue if they try to buy again. Want to prevent people from obtaining multiple queue positions by using multiple devices or browsers? That's a snap with our Join Token feature too, so you really can ensure one order per customer - and one queue position per customer - with Queue-Fair.
Last and by no means least, unlike waiting rooms from other providers (Source: discountcodes.org.uk), visitors cannot bypass Queue-Fair security by pretending to be Google. And again unlike other online queue management systems from other providers, with Queue-Fair Google and other search engines can crawl your site unimpeded without compromising security.
 Keep your website open, regardless of demand
Keep your website open, regardless of demand